Cybercrime is evolving faster than many organizations can respond. The recent takedown of the notorious LeakBase forum by Europol highlights just how organized and sophisticated underground data trading has become and why enterprises need to rethink their approach to data governance.
LeakBase, active since 2021, operated as a central hub for stolen credentials and breached databases, catering to over 142,000 registered users worldwide. It specialized in “stealer logs”, archives of usernames, passwords, and other access credentials harvested through malware. Accessible on the open web, the forum enabled cybercriminals to buy, sell, and exchange sensitive data, creating a thriving, reputation-driven economy.
Coordinated Global Enforcement: Operation LEAK
Between 3 and 4 March 2026, law enforcement agencies across multiple jurisdictions launched Operation LEAK, a coordinated effort to dismantle the forum and target its most active users. This included:
- Around 100 enforcement actions globally
- Arrests, house searches, and “knock-and-talk” interventions targeting 37 key users
- Technical disruption, including seizure of the forum’s domain and replacement with a law enforcement splash page
As Edvardas Šileris, Head of Europol’s European Cybercrime Centre, emphasized, “No corner of the internet is beyond the reach of international law enforcement. Those who believed they could hide behind anonymity are being identified and held accountable.”
Implications for Enterprises
This takedown serves as a stark warning for organizations of all sizes. Data breaches do not simply disappear. They often end up on criminal platforms like LeakBase, where they can be reused for identity theft, fraud, account takeovers, or phishing attacks.
Enterprises now face a dual challenge:
- Preventing breaches in the first place
- Mitigating the impact if data is exposed
Key strategies include Governance gap of data breaches in 2026:
- Enforcing strong password policies and multi-factor authentication
- Monitoring cloud and third-party access for misconfigurations
- Regularly auditing sensitive data to ensure minimal exposure
Lessons from LeakBase
- Credential Protection is Critical
LeakBase’s primary commodity was login credentials. Enterprises should adopt proactive zero-trust strategies, using solutions that monitor credentials for signs of compromise. - Operational Visibility Matters
Europol’s success was partly due to cross-border intelligence sharing and real-time monitoring. Similarly, organizations need tools to track sensitive data movement and respond immediately to suspicious activity. - Prevention Over Reaction
As the operation moves into its prevention phase, it underscores the importance of real-time safeguards. Using solutions like how Trust-Prompt works, organizations can intercept sensitive data before it leaves internal systems.
Strengthening Enterprise Defenses

For enterprises operating in Europe, GDPR compliance remains essential. Beyond legal requirements, adopting a proactive local-first security approach ensures sensitive information stays on your network, reducing exposure to external threats. For more guidance, see our EU AI Compliance and Governance guide.
Additional tools like Trust Prompt Plus provide automated filters to catch high-risk data in real-time, bridging the gap between compliance and operational efficiency.
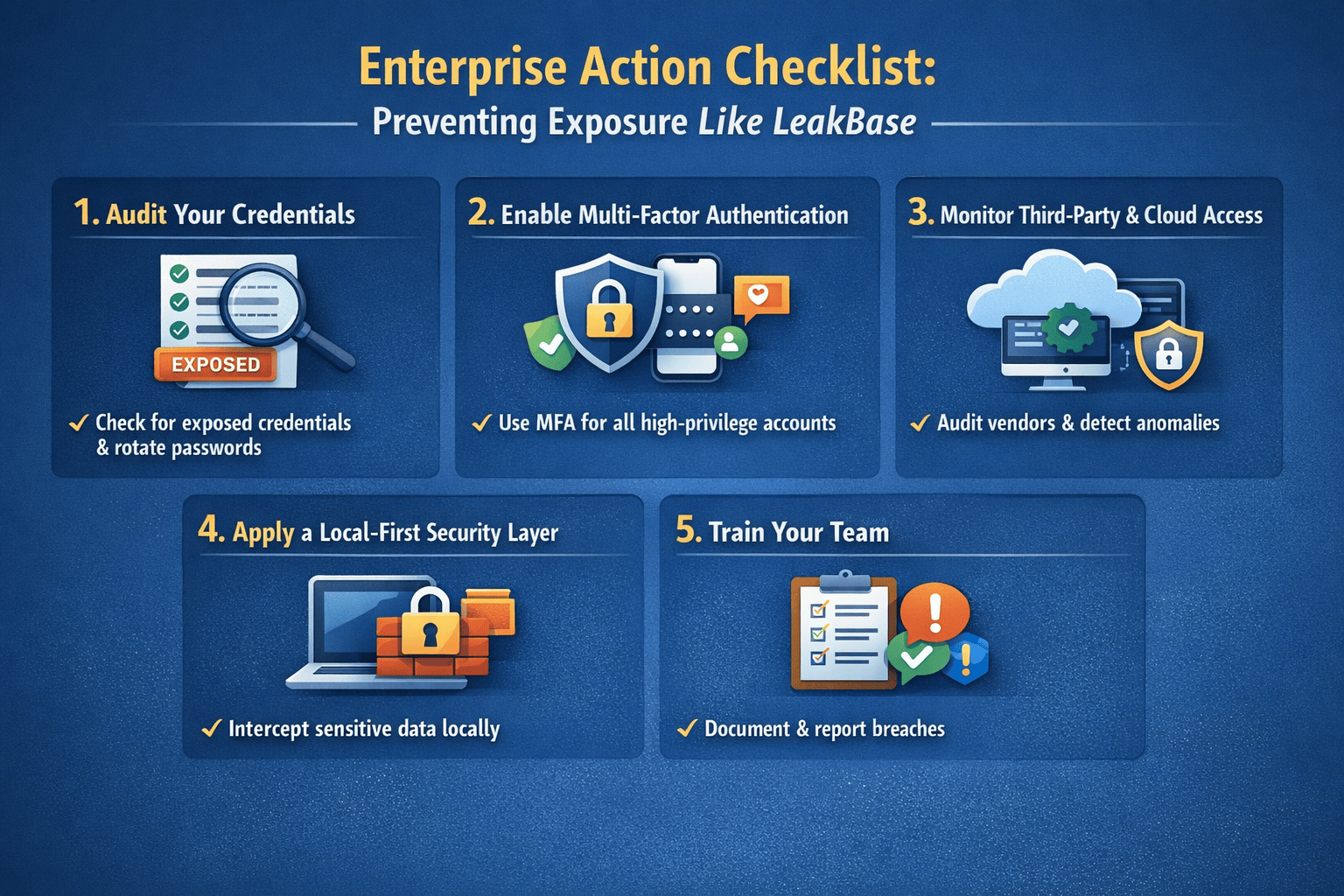
Enterprise Action Checklist: Preventing Exposure Like LeakBase
To translate lessons from Europol’s operation into practical enterprise action, consider these steps:
- Audit Your Credentials
- Regularly check for exposed credentials in public databases and dark web sources
- Enforce rotation and strong password policies
- Enable Multi-Factor Authentication (MFA)
- Critical for all accounts, especially high-privilege users
- Monitor Third-Party and Cloud Access
- Audit vendor and SaaS access
- Ensure proper permissions and real-time anomaly detection
- Apply a Local-First Data Security Layer
- Intercept sensitive data before it leaves endpoints
- Use automated tools to flag personal, financial, or restricted data
- Train Your Team
- Conduct workshops on phishing, credential safety, and secure data handling
- Promote awareness that stolen data can resurface on platforms like LeakBase
- Prepare a Response Plan
- Document breach response protocols
- Ensure compliance with GDPR reporting timelines
Takeaway
The LeakBase dismantling is a reminder that cybercriminals are sophisticated, global, and relentless. Enterprises must move beyond reactive security measures. By combining strong governance, technical prechecks, and cross-border intelligence insights, companies can protect both their customers and their reputation in an increasingly hostile digital landscape.
For more updates, check out our News section.
External references supporting this article:

Very good i like it