If the last decade was about digital transformation, 2026 is about digital tension. The world is more connected than ever, yet also more fragmented. Cybersecurity is no longer just a technical concern sitting inside IT departments. It has become a core part of geopolitics, business strategy, and even everyday life.
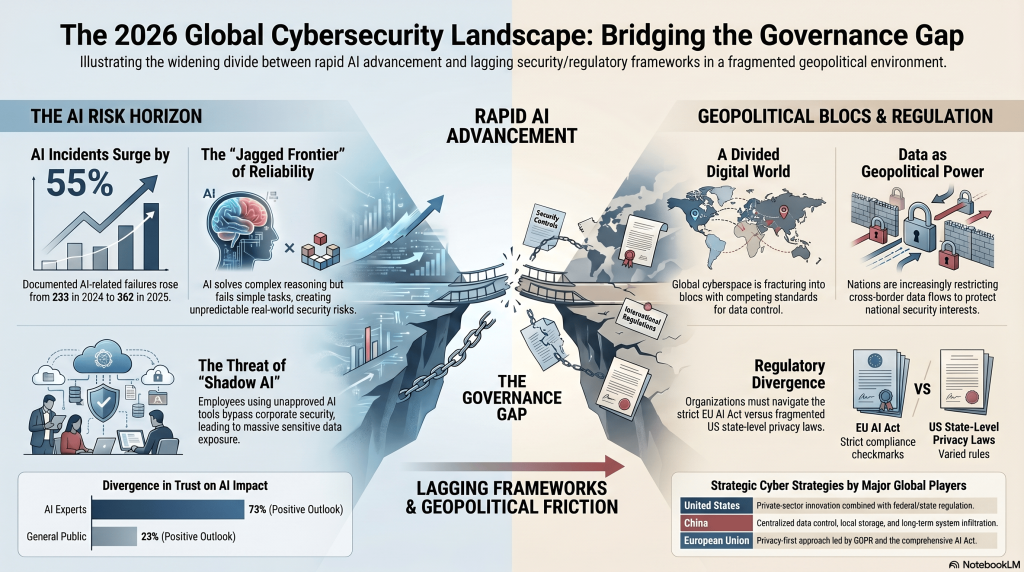
What makes this moment stand out is the convergence of several forces: rising geopolitical conflicts, rapid advances in artificial intelligence, and an increasing number of data breaches. Add to that a growing web of global regulations, and you get a landscape that is both innovative and deeply unstable.
This is the reality organizations and individuals are operating in today.
Cyber Warfare Is No Longer Hidden in the Background
Not long ago, cyberattacks were seen as isolated incidents such as ransomware or data leaks. Today, they are tightly woven into geopolitical conflicts. The tensions involving Iran, the United States, and Israel show how cyber operations are used to disrupt infrastructure, gather intelligence, and influence public perception.
Cyberattacks often take place before physical military actions even begin. They weaken communication systems, create confusion, and reduce the effectiveness of traditional defenses. What makes them powerful is that they operate below the threshold of open war, making retaliation difficult.
This has turned cyberspace into a constant battlefield. Many of these attacks never make it into the daily News cycle, but they are happening continuously in the background.
The Big Players and How They Operate in Cyberspace

Each major power has developed its own cyber strategy. The United States combines strong government capabilities with leading private-sector innovation. Israel is known for highly targeted and precise cyber operations backed by deep intelligence expertise.
China focuses on long-term access. Instead of immediate disruption, it often aims to quietly infiltrate systems and remain undetected. Russia has built a reputation for disruptive operations, especially against infrastructure and political systems. Iran uses asymmetric tactics, relying on proxy groups and large-scale campaigns to create pressure.
Other countries such as India, Turkey, and Saudi Arabia are building their capabilities while trying to maintain strategic independence in a divided digital world.
Artificial Intelligence Is Changing the Rules of Cybersecurity
Artificial intelligence is now a central part of cybersecurity on both sides of the equation. It helps defenders detect threats faster, but it also gives attackers new tools to operate at scale.
AI can automate phishing campaigns, generate highly convincing fake content, and identify system vulnerabilities in seconds. At the same time, organizations use AI to monitor networks and respond to threats more efficiently.
The AI Index Report 2026 highlights how quickly AI adoption is growing. This growth is driving innovation, but it is also increasing the speed and complexity of cyber threats.
Why Data Has Become a Form of Power

Data is no longer just a business asset. It has become a source of geopolitical power. It fuels artificial intelligence, supports economic growth, and enables intelligence operations.
Because of this, countries are becoming more protective of their data. Many are introducing laws that restrict how data can be stored and transferred across borders.
When data is exposed through breaches, the impact goes far beyond financial loss. It can influence markets, compromise security, and damage trust on a large scale.
The Reality of Data Breaches Today
Data breaches are now a regular occurrence, but their impact continues to grow. Incidents such as the Fiverr Data Leak show how vulnerabilities in widely used platforms can expose large amounts of sensitive information.
These breaches often happen due to a combination of technical weaknesses and human error. Once data is exposed, it can spread quickly and be used for fraud, identity theft, or further cyberattacks.
For organizations, the consequences are serious. They face regulatory fines, legal challenges, and long-term reputational damage.
The Hidden Risk of Shadow AI in Organizations
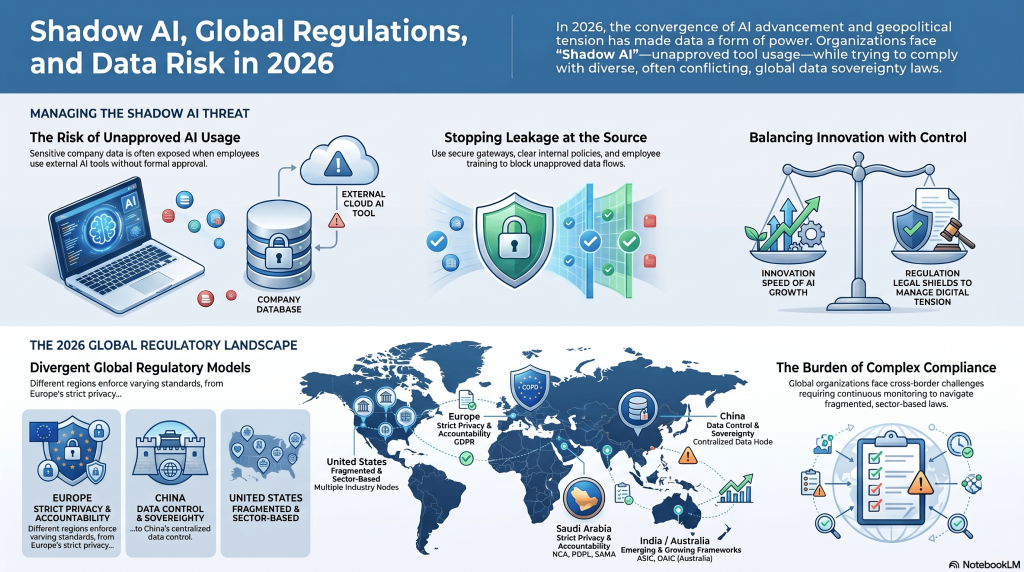
A growing challenge for many companies is the rise of Shadow AI. Employees are increasingly using AI tools without formal approval, often to improve efficiency or productivity.
While the intention is usually positive, the risks are significant. Sensitive data can be shared with external systems without proper safeguards.
This is why Stopping Shadow AI at the Source has become a key focus. Organizations need clear policies, secure internal tools, and ongoing education to reduce this risk.
Regulations Are Catching Up with Innovation
Governments are working to address these challenges through new regulations. The idea of News balancing innovation with regulations reflects the effort to encourage technological progress while protecting users and systems.
Different regions are taking different approaches. Some prioritize strict oversight, while others focus on flexibility and innovation.
For global organizations, this creates a complex environment where compliance is not straightforward and requires constant attention.
Europe’s Strong Push on Privacy and Cybersecurity
Europe has taken a leading role in digital regulation. The General Data Protection Regulation has set a global standard for privacy. Additional frameworks expand this focus to include cybersecurity and operational resilience.
The European approach emphasizes accountability and strong enforcement. This has pushed organizations around the world to improve their data protection practices.
The United States and Its Complex Regulatory Landscape
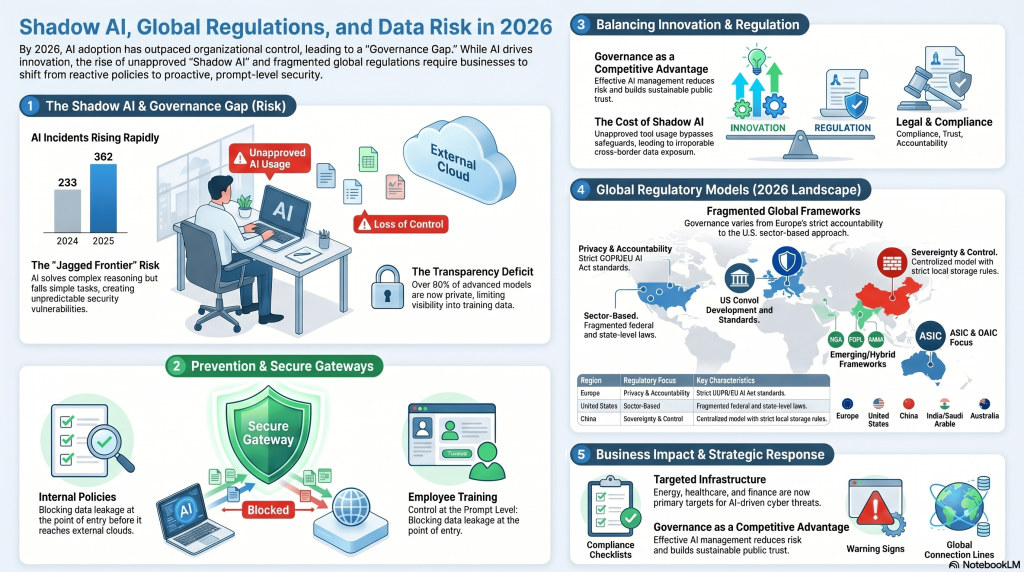
The United States uses a mix of federal and state-level regulations. This approach allows flexibility but also creates complexity.
Different industries are governed by different rules, and states have introduced their own privacy laws. Enforcement is strong, but the lack of a unified framework can make compliance challenging for organizations operating across multiple regions.
China’s Approach to Data Control and Security
China has developed a centralized model focused on data control and national security. Regulations require companies to store data locally and follow strict rules for transferring it abroad.
This approach gives the government significant oversight of data flows. For businesses, it means navigating a highly regulated environment with strict compliance requirements.
Emerging Markets Are Shaping Their Own Models
Countries such as India and Saudi Arabia are building their own regulatory systems. These frameworks often combine elements from different global models.
India is focusing on strengthening its digital economy while introducing new data protection laws. Saudi Arabia is investing heavily in cybersecurity as part of its broader transformation strategy.
These regions are becoming increasingly important in the global digital landscape.
Critical Infrastructure Is the Primary Target
Cyberattacks are increasingly targeting critical infrastructure. Energy systems, healthcare networks, and financial institutions are all at risk.
Disruptions in these areas can have immediate and serious consequences, affecting both economies and public safety.
Governments are responding by increasing investment in security and introducing stricter regulations to protect these systems.
The Next Wave of AI-Driven Threats

The role of artificial intelligence in cyber threats is expected to grow even further. Future attacks may become more automated, more adaptive, and harder to detect.
At the same time, defensive technologies will continue to improve. This creates an ongoing cycle where both attackers and defenders are constantly evolving.
Organizations need to stay ahead by adopting advanced security strategies and continuously updating their defenses.
A World Divided into Digital Blocs

The global digital landscape is becoming more divided. Different regions are developing their own standards, technologies, and policies.
Western countries tend to support open but regulated systems, while others focus on greater control over data and infrastructure.
This division affects how data moves across borders and how companies operate internationally.
What Organizations Need to Do Now
Organizations can no longer afford to take a reactive approach to cybersecurity. They need to focus on resilience.
This means building strong security systems, understanding regulatory requirements, and preparing for potential disruptions. It also involves training employees and creating a culture of awareness.
Cybersecurity is no longer just about prevention. It is about being ready to respond and recover.
Conclusion – Building Trust in an Uncertain Digital World
The intersection of geopolitics, cybersecurity, and artificial intelligence defines the world in 2026. Conflicts involving Iran, the United States, and Israel show how digital capabilities are now central to global power.
At the same time, data breaches, evolving threats, and complex regulations create new challenges for organizations and individuals.
Building trust in this environment requires a combination of strong technology, clear governance, and continuous awareness. Those who understand and adapt to these changes will be better prepared for the future.
